There are more devices in today’s market than ever before. According to Statista, “The number of Internet of Things (IoT) devices worldwide is forecast to almost double from 15.1 billion in 2020 to more than 29 billion IoT devices in 2030.” These IoT devices range from your smartphone and computer to the exercise tracker you wear and touch screen in your car. Anything that has the ability to collect data in real-time and connect to a network is in the IoT.
But what does an increase in devices mean for cybersecurity?
In today’s interconnected world, where devices and networks are seamlessly intertwined, endpoint security has become a top concern for organizations of all sizes. An endpoint is any device connected to a network that can send or receive communications, including smartphones, desktop computers, servers, and more. These devices are vulnerable because of their network connection, data processing, and communication capabilities.
Endpoint security, the practice of safeguarding these devices, has undergone a remarkable transformation in recent years, adapting to the ever-changing landscape of cyber threats.
Early Days: Signature-Based Antivirus
In the 1980s antivirus software was developed to detect and contain malware within endpoints. These programs would search the device’s CPU for signatures of known malware, known as fingerprint detection. However, these technologies could only protect against known malware signatures and no real-time updates were available as new risks were identified.
Next-Generation Antivirus (NGAV): Beyond Signatures
As cyber threats grew more sophisticated and malware threats increased in the 2000s, signature-based antivirus proved inadequate. Next-generation antivirus (NGAV) emerged as a more proactive approach, employing a combination of techniques, including sandboxing, machine learning, and behavioral analysis, to detect and neutralize even unknown threats.
NGAV shifted the focus from identifying specific signatures to analyzing the behavior of software and data, providing a more comprehensive defense against evolving threats.
Protection, Detection, and Response
Endpoint protection platforms (EPPs) were introduced in the early 2000s to combine antivirus, encryption, vulnerability assessment and more to respond to dynamic security incidents and alerts. Additionally, EPP is often paired with endpoint detection and response (EDR) solutions. EDR extends beyond mere detection, offering deeper visibility into endpoint activities and the ability to investigate and respond to potential threats. EDR solutions collect and analyze endpoint data, providing security teams with insights into user behavior, network traffic, and system events, enabling them to identify and mitigate threats before they cause significant damage.
The Modern Age of Endpoint Protection
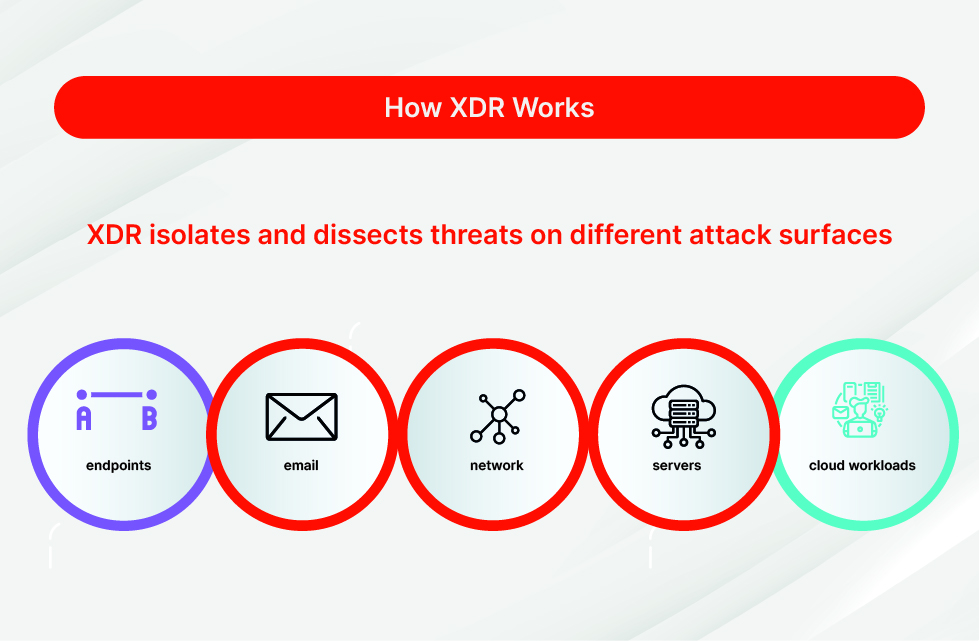
The concept of extended detection and response (XDR) was first introduced by Palo Alto Networks in 2019. XDR platforms typically allow for multi-domain security tracking, threat detection, analysis, and prioritization as well as responses to mitigate and remediate the threat. A true XDR solution integrates multiple data sources into a single platform for easier analysis and remediation.
Zero Trust: A Paradigm Shift
Zero Trust, a security model that assumes no user or device is inherently trustworthy, represents a shift in endpoint security. This approach emphasizes continuous verification and access control to ensure that only authorized users and devices can access sensitive resources. Zero Trust principles should be integrated into both endpoint and network security, creating a holistic protection. This is completed by implementing the Zero Trust model across all security architectures.
The Future of Endpoint Security
As we look ahead, endpoint security managers are navigating a rapidly changing landscape. The constant evolution of cyber threats necessitates continuous innovation endpoint protection services.
The future of endpoint security is characterized by the integration of artificial intelligence (AI), automation, and machine learning. As AI-powered threat detection and response become more sophisticated, enabling real-time identification and neutralization of threats, incident response processes will be streamlined, reducing the burden on security teams and minimizing the impact of cyberattacks.
Unified endpoint security platforms, such as true XDR solutions, will integrate various security tools, provide a holistic view of endpoint security posture, and enable centralized management.
Endpoint protection services are not only about preventing malware; it is aimed at developing a holistic approach to protecting your data, warding off persistent threats, and ensuring the overall resilience of organizational IT infrastructures. The journey of endpoint protection from the rudimentary antivirus solutions of the 1980s to the sophisticated, multifaceted platforms of today reflects the ongoing arms race between cybersecurity professionals and malicious actors. As we undergo future developments, collaboration, innovation, and an understanding of emerging threats will fortify the defenses of endpoint security in the years to come.
Your Next Step? Chat with Liquid Networx.
Protected endpoints give you and your business peace of mind. Learn more about how to protect your devices and data by contacting our team.
